Why use a password manager when you can throw all passwords into a sticky note? Well, think of it this way: unless you enjoy playing Russian roulette with your digital (and real) life, a password manager is a must.
Password managers do more than just provide a safe haven for your passwords. Multiple data breaches occur every single week, impacting thousands of users. While a password manager can’t prevent data breaches, it can protect your identity with features like breach monitoring and generating discardable emails and phone numbers.
And that’s just the tip of the iceberg. Let’s take a look at why you should be using a password manager, how they keep you safe online, and how to choose the best password manager for you.
What is a Password Manager?
Imagine a digital safe where you can securely store your passwords with multiple layers of protection like encryption and multi-factor authentication (MFA). That’s a password manager!
Modern password managers do more than just protect your passwords. They also:
- Generate complex passwords
- Identify weak or reused passwords
- Auto-fill passwords on web pages
- Sync passwords among devices
They may also offer additional security and privacy features, such as how Cloaked can send one-time passcodes, store additional personal information, and much more.
Benefits of Using a Password Manager
From major brands like Sony, 23andMe, and Comcast to the U.S. State Department, many institutions suffer from data breaches every year.
A password manager can ensure these data breaches don’t cost you your privacy or, in the worst cases, a ton of money.
Here are the benefits a password manager offers in addition to protecting your privacy and money:
1. Comprehensive Password Management
You can kiss your password management woes goodbye once you hand them over to a password manager. A password manager:
- Generates complex passwords: 66% of Americans use the same password for multiple accounts. But with a password manager, you don’t have to generate complex passwords yourself or worry about remembering them. The best password managers generate complex passwords according to the guidelines in NIST Special Publication 800-63B.
- Stores passwords: Password managers store your passwords and sync them across devices so you don’t have to scribble every password on a sheet and refer to it whenever you want to log in.
- Protects your passwords: Password managers encrypt your passwords to protect them. Only your password manager knows how to decrypt a password, which means even if someone manages to hack into your network, they won’t be able to read your passwords.
- Audits your passwords: Password managers help you find weak, old, or duplicated passwords. It scans your passwords against known password databases and when there’s a match, it prompts you to change that password.
2. Login Auto-Filling
Password managers are always on high alert when you’re browsing. When you land on a webpage that has the username, email, and password fields, the password manager springs into action.
Depending on the device you’re using, the browser extension or the app taps into the vault and finds the right credentials.
Some password managers go a step further and eliminate the need to click on the login button. This is possible when the password manager communicates with the browser via application programming interfaces (APIs).
This feature can help prevent credential stuffing attacks. In credential stuffing, cybercriminals use automated tools to try username and password combinations sourced from data breaches on other websites. The idea is to misuse the average user’s tendency to reuse passwords across multiple accounts.
For example, the 23andMe data breach happened using credential stuffing tactics: hackers used stolen passwords from one account to gain access to other accounts that were using the same login information.
Threat actors that are using stolen credentials don’t have to worry about evading threat detection systems or deploying complex ransomware: they can just log in to a user’s account using the username and password they stole from another account.
When your password manager generates, manages, and autofills long and complex passwords for you, you never need to reuse the same credentials. This keeps all of your different accounts secure–even if one gets compromised.

Learn about Cloaked’s password manager
3. Cross-Platform Syncing & Compatibility
Suppose you use a password manager on your laptop and phone. You added a new account to the password manager this morning. You want to log into that account with your smartphone but you don’t have access to the laptop.
Password managers make it happen. Here’s how:
- Encryption: The password manager encrypts your new account’s credentials using complex algorithms and encryption ciphers.
- Cloud server: The password manager sends this encrypted data to a cloud server. Whenever you add, delete, or modify credentials in the password, it makes the same change on the cloud server.
- Sync with a smartphone: The phone app syncs with the cloud server, giving you access to credentials for your new account.
The best part? All of this happens in an instant.
4. Secure Sharing
Some password vaults allow you to create a shareable link for a digital handoff of specific passwords in your vault to another person. When the person opens the link, they authenticate themselves using their own master password to access the password.
You’re always in full control of access—you can edit or revoke access at any time. Some password managers also allow you to track who accessed which password and when–creating a digital audit trail.

Cloaked identity sharing is a secure method for giving out information with end-to-end encryption.
5. Information Storage
Password managers store more than just login credentials. You can also store notes, credit card details, and confidential documents.
Almost everything that applies to passwords also applies to other information. Password managers:
- Encrypt information using advanced algorithms
- Let you control access to the information
- Securely sync information with a cloud server
With your Cloaked identities, you can store anything you need securely and in one place. Bank account info, addresses, API keys–anything you need. When you need to share info with friends and family, you decide exactly who can access it and when.

6. Additional Features
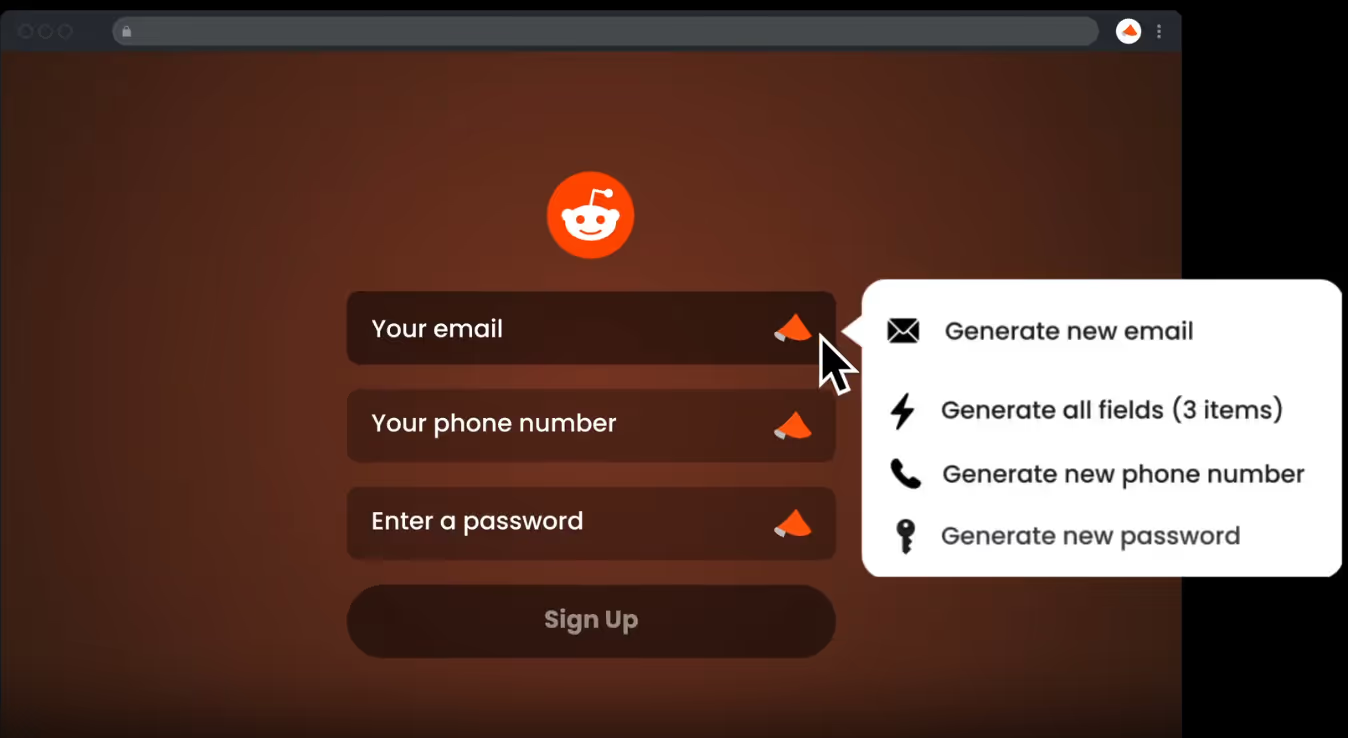
Some password managers offer additional privacy features. For example, Cloaked is an all-in-one savior for your digital privacy, offering various security features such as its AutoCloak capability, which turns all your old passwords and logins into secure Cloaked identities.
An online identity includes your personal information—email, password, phone number, and more. Suppose you have a Fidelity banking account and you want to replace your original information in the Fidelity account with an identity generated using Cloaked. To do this, you go into your dashboard, select the identities you want to AutoCloak, and Cloaked updates everything for you.
But don’t stop with Fidelity! Cloaked allows you to batch-replace multiple identities all at once with secure email addresses, phone numbers, usernames, and passwords.

Best Practices for Using a Password Manager
A tool is only as powerful as the hands that wield it. Here are a few best practices to be mindful of for maximum security:
Skip Native Password Managers
Native password managers are convenient because they’re often easily accessible. But using Chrome’s built-in password manager or the Credential Manager in Windows, for example, has some extensive risks:
- Tied with device’s security: Native password managers are intertwined with your browser or device’s security. If someone gains access to your device, they might get a free pass to your passwords. It’s like leaving your keys under the doormat—convenient, but unsafe.
- Inadequate security: Native password managers may use older encryption ciphers. In fact, Google Password Manager uses closed-source code and offers no information about its security architecture.
- Lack of features: Third-party password managers offer a robust feature set, including features like security audits and breach monitoring. Most native password managers are limited to basic features like password storage and password generation.
Choose a Strong Master Password
Choosing a strong master password is like fortifying the gates of your digital fortress. The more formidable your master password, the harder it will be for an attacker to get access to your passwords.
Here are some basics to follow:
- Use long and complex passwords: Complex passwords include multiple character types, including numbers, symbols, and letters. Aim for passwords at least 12 characters long.
- Avoid common passwords: Adversaries use dictionary attacks which involve using pre-existing lists of common passwords or phrases to guess your password. That’s exactly why NIST recommends that you avoid using common passwords.
- Use authentication factors: Use MFA whenever possible. MFA adds more layers of security that make it harder for adversaries to get through to your vault.
Protect Your Physical Devices
Accessing your passwords isn’t impossible if someone gets physical access to your device. It’s like breaking through the gate of your fortress—challenging, but it can happen. Here’s what you can do to protect your device:
- Device security: Limit physical access to your device and make sure to lock the device when not in use.
- Update your device: Update your operating system, apps, and password manager to protect your device against known vulnerabilities.
- MFA: MFA features like biometric authentication and time-based one-time passwords (TOTP) add more security layers, making it harder to gain unauthorized access.
Improve Your Overall Password Habits
Practicing good password hygiene can make a world of difference. Here are a few good password habits you should follow:
- Don’t write down passwords: Avoid writing your passwords on sticky notes. It’s never a good idea to have your passwords stored in plain text, whether that’s on physical paper or in Google Sheets.
- Don’t share your password: Don’t share your password unless necessary. When you do have to share a password, share it via your password manager, never in plain text.
- Change passwords as needed: Top password managers offer built-in breach monitoring. When the password manager finds your password in a data breach, it alerts you. This is your queue to change the password.
- Educate yourself and be vigilant: Don’t click on links you don’t trust. Don’t enter your details on pages you don’t trust. Continue to educate yourself about ways to protect yourself online.
Risks of Using a Password Manager
Password managers are built to minimize risk. However, you still need to follow best practices to protect your data. Here are the risks to consider when using a password manager:
- Password managers without 2FA: One of the biggest risks of using a password manager is also the reason why most people use password managers—convenience.
The problem with password managers is that they store all passwords in one secure place so it’s convenient for you to access them. But hackers want the exact same thing—all your data in one place. This makes device security mission-critical. Unless you use 2FA, you risk your password’s security.
Picture this. You’re using your phone when riding the subway and someone is looking over your shoulder. They memorize your device’s four or six-digit unlock code. The next time you put your phone down—whether at the market or at the restaurant—the criminal can pocket your device and gain access to all your passwords.
- Device security: A device’s physical security isn’t the only thing you need to worry about. Hackers also use techniques like malware, phishing, SIM swaps, and WiFi hijacking.
If a hacker manages to infect your device with malware, it will record your password as you type it. To prevent this, use a good antivirus program and don’t click on random links.
The only way to minimize the risks of a password manager is to use a password manager like Cloaked, which offers top-notch security and an extensive feature set.
Cloaked protects you against these adversaries with features like 2FA and advanced algorithms and encryption ciphers like ECC25519, Argon2, and XSalsa20-Poly1305. So even if a threat actor gets access to your device, they won’t get access to any of your logins, passwords, or saved information on Cloaked.
How to Choose the Right Password Manager
Since choosing the right password manager is vital to your password’s security, here’s a quick guide on how to choose a password manager.
1. Assess Security Features & Risk Responsiveness
Consider the following to assess the security features and risk responsiveness of a password manager:
- Encryption standards: Look for string encryption ciphers like AES-256 or ECC25519. Strong encryption ensures that hackers can’t read your passwords, even if they manage to intercept your network and get their hands on it.
- MFA: Check if your password manager supports MFA so you can add more layers of security beyond the master password.
- Breach response: Assess the provider’s response to breaches. Choose providers that are transparent in communicating the breach and demonstrate commitment to security.
2. Review Privacy Policy & History
Consider the following when reviewing the privacy policy and history:
- Look for details: When assessing the privacy policy, look for details on encryption, data-sharing practices, the way the provider handles user information, and whether the provider sells user data. Pay attention to the parts that discuss data retention and how they handle requests for user data.
- Research the company: Check the provider’s track record for security incidents and data breaches. Check if the company has independent reviews, transparency reports, and security audits that show their commitment to user’s security and privacy.
- User reviews: Read reviews from users on forums and other reputable sources.
- Compliance with data regulations: Ensure the password manager complies with your region’s data protection laws like GDPR (General Data Protection Regulation).
3. Prioritize User Experience
Convenience is one of the primary reasons for using a password manager. If the app makes you jump through hoops to set up and access your passwords, it defeats the purpose of investing in a password manager.
Look for a password manager that:
- Is easy to set up
- Has an intuitive user interface
- Offers an extensive feature set
- Has various help resources, FAQs, and customer support
4. Look for Comprehensive Password Manager Features
Most password managers from reputable providers offer the basics—password generation, strong encryption, what have you. But the top providers offer one or more of the following features to up your password game and online security:
- Emergency access for a designated trusted contact
- Dark web monitoring to scan for your credentials in data breaches or illicit websites
- Encrypted file storage to store documents and other files
5. Consider Additional Privacy Features
In addition to a transparent privacy policy, look for the following privacy features:
- Zero-knowledge architecture to ensure not even the provider has access to your decrypted data
- Local-only encryption for data you don’t want to transmit to a cloud server
- Anonymous account creation so you can create an account without sharing personal information
- Secure sharing so you can share access to an account without revealing the password
6. Read User Reviews
Read user reviews on forums and review websites like Capterra to understand what users think about the password managers you’ve shortlisted. Look for insights on the following:
- Overall satisfaction
- Security and privacy
- Ease of use
- Features and functionalities
- Customer support
- Common problems
7. Review Pricing & Plans
Before you pull out your credit card, take a pause and see if the provider offers enough value—does it offer a good enough feature set and customer support given the price you’re paying? More importantly, is the price within your budget?
If the value and budget aren’t a problem, check if the app offers a trial or freemium plan. This gives you a chance to use the app firsthand without risking any money.
Some providers offer better rates for family or group plans. If your family members plan to use the password manager as well, these might be worth exploring.
Protect Yourself with the Best Password Manager
Choosing the best password manager isn’t just about security. It’s a proactive stance against the wide range of threats lurking in the digital world. That’s where Cloaked comes in.
Cloaked makes it easy to generate complex passwords and store them in a digitally secure vault. The platform’s robust encryption ensures your passwords never go into the wrong hands.
And that’s not all—Cloaked offers nifty features like AutoCloak that help generate an email, password, phone number, and more, so you never have to share your private information.
Leave your passwords with a reliable partner.










