Why Phone Aliasing Matters in Modern Digital Privacy
Phone numbers have quietly become one of the most dangerous pieces of Personally Identifiable Information (PII) a person can share. Unlike email addresses — which can be replaced, ignored, or redirected — a phone number is deeply tied to authentication, banking, recovery access, messaging platforms, and identity verification systems.
Once exposed, it can trigger:
- SIM-swap attacks
- spam calls
- social profiling
- two-factor authentication interception
- cross-platform identity linking
- and real-world traceability
In a world where people operate across social apps, online dating, ride-share services, forms, subscriptions, and marketplace listings, having only one primary phone number creates unnecessary risk.
This is where phone aliasing — the ability to use alternate numbers — becomes a crucial privacy layer. The challenge is:
Which services let people stay anonymous without sacrificing reliability, SMS functionality, or communication convenience?
What Is Phone Aliasing? A Clear Foundation
Phone aliases
These are secondary numbers that act as a proxy between your real phone number and the outside world. They allow calling and texting without revealing your identity.
2-way communication
A proper alias should allow SMS and voice both ways — not just outbound masking.
Authentication support
Many services fail during 2FA verification because certain numbers aren’t accepted by banks or platforms.
Persistence
Disposable numbers are helpful for sign-ups, but business cases require long-term stability.
Phone aliasing is no longer just about privacy — it’s about maintaining identity separation without losing functionality.
The Market Landscape: Types of Phone Alias Tools
Burner-style disposable apps
Short-term, temporary phone numbers ideal for short projects and online listings.
Strength: anonymity
Weakness: lifespan + reliability
Secondary number communication apps
Tools like Hushed that offer monthly virtual numbers with calling + texting.
Strength: usability
Weakness: limited identity separation features
Voice-over-IP ecosystems
Large platforms like Google Voice that focus on convenience, not anonymity.
Strength: integration + cost
Weakness: privacy trade-offs
All-in-one identity masking platforms
Solutions combining alias phone, email, address, payment masking, secure storage, and identity generation tools.
Strength: privacy depth
Weakness: broader ecosystem complexity
This spectrum matters when deciding between privacy versus convenience.
How Today’s Phone Alias Tools Compare
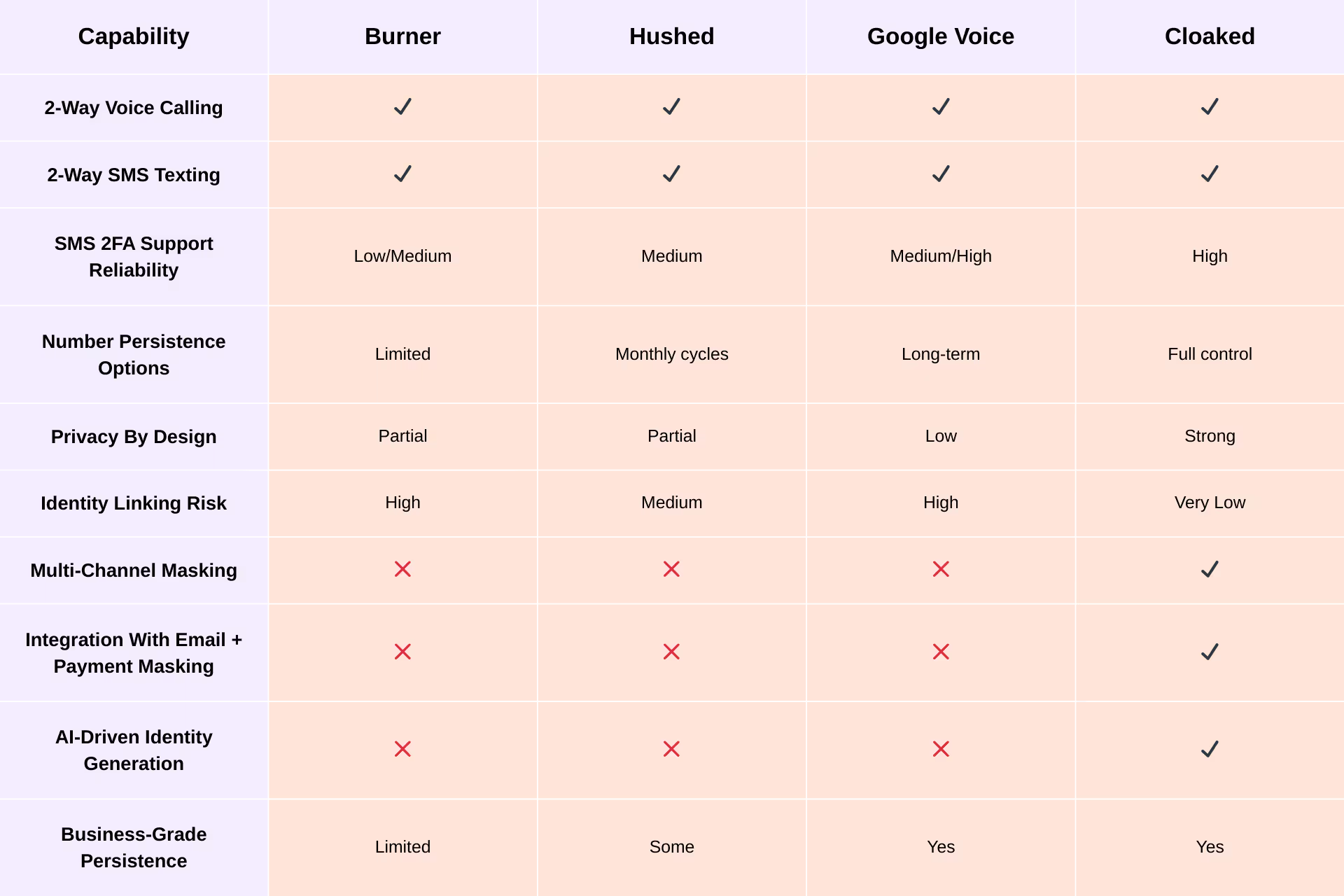
Deep Comparison Across Competitors
Burner
Burner provides temporary numbers intended for short-term use.
Perfect for classified ads or quick engagements, but less suited for:
- long-term communication
- business messaging
- identity continuity
Most Burner numbers expire within set periods, and SMS authentication success rates vary.
Hushed
Hushed offers month-to-month secondary numbers across multiple regions.
It works well for:
- travel
- casual communication
- online privacy
However, Hushed does not specialize in identity protection. Numbers still connect back to user accounts through logged metadata.
Google Voice
Google Voice leans toward integration and convenience rather than anonymity.
Strengths include:
- voicemail
- long-term number ownership
- Google ecosystem syncing
But because the number is tied to a Google identity, it does not provide true anonymity, and metadata trails remain extensive.
Cloaked
Cloaked takes a different approach — instead of offering another communication app, its phone aliasing lives within a full identity separation system.
Users can:
- generate persistent phone aliases for business
- create short-term numbers for one-off signups
- keep aliases active indefinitely
- run voice + SMS channels
- reduce identity tracing
- support 2FA reliability
- link numbers to masked emails + masked payments
Because phone aliases sync with identity masking, Cloaked minimizes metadata exposure and reduces the chance of cross-platform tracing.
This makes Cloaked a strong option where privacy matters as much as function.
Best Use Cases for Each Tool
Short-term anonymity
Burner fits quick selling, classifieds, and temporary conversations.
International flexibility
Hushed works well for SMS/calling in non-US regions.
Personal productivity + voicemail
Google Voice fits users who simply want a unified phone experience.
Long-term persistent identity separation
Cloaked is ideal for:
- business communications
- platform verification
- multi-identity environments
- user verification with 2FA
Because Cloaked numbers sit inside a larger identity ecosystem, the privacy benefit multiplies beyond the phone layer.
Snapshot: What Each Tool Is Best At
- Burner → ideal for quick, throwaway numbers
- Hushed → flexible, region-friendly phone layering
- Google Voice → great for free long-term call and text usage, not privacy
- Cloaked → strong for persistent aliasing, real anonymity + identity protection
Making the Right Choice: Function vs Anonymity
Phone aliasing isn’t just a convenience feature anymore — it’s a core part of digital identity control.
If your priority is price and simplicity, communication-first apps like Google Voice and Hushed work well.
If your need is fast, temporary anonymity, Burner fits.
But if you want:
- stable alias numbers,
- reliable SMS 2FA support,
- business capability,
- minimal metadata logging,
- multi-channel identity masking,
- and separation between real identity and communication…
then platforms designed around privacy architecture — not just communication routing — provide greater long-term value.
Cloaked fits that category by enabling people to manage communication without revealing real phone numbers, while aligning with broader identity separation.